Security Affairs newsletter Round 428 by Pierluigi Paganini – International edition
Security Affairs
JULY 15, 2023
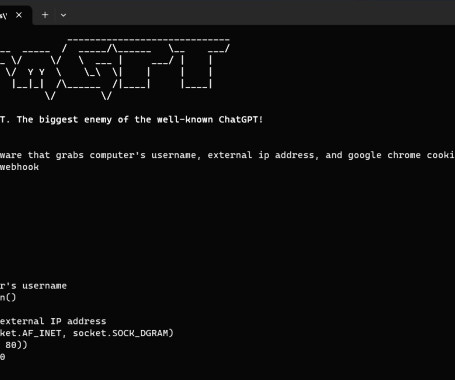
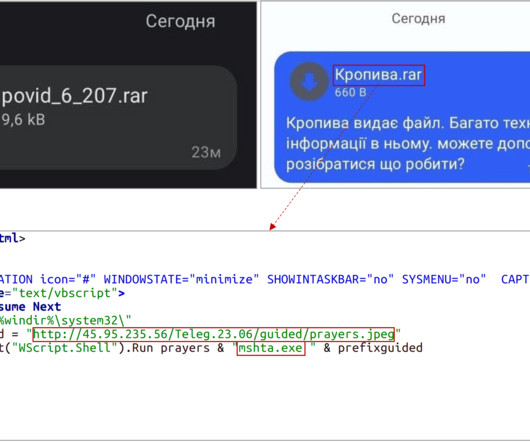
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial compromise The source code of the BlackLotus UEFI Bootkit was leaked on GitHub US CISA warns of Rockwell Automation ControlLogix flaws Indexi













Let's personalize your content