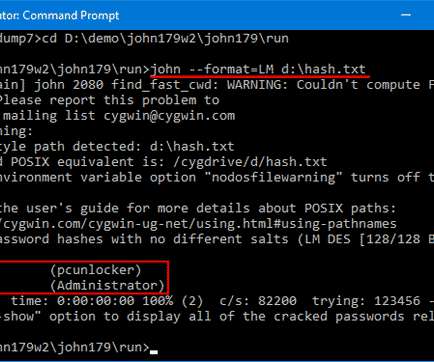
John the Ripper: Password Cracking Tutorial and Review
eSecurity Planet
JANUARY 31, 2023
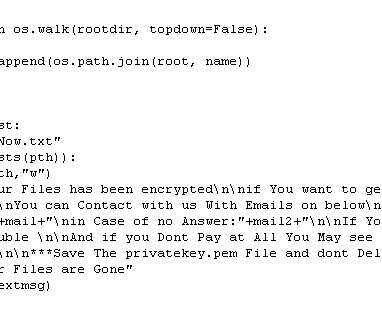
John the Ripper is a popular password cracking tool that can be used to perform brute-force attacks using different encryption technologies and helpful wordlists. It’s often what pen-testers and ethical hackers use to find the true passwords behind hashes. For our example, we won’t need a powerful machine.
























Let's personalize your content