Beyond the Office: Securing Home Devices and Networks Against Corporate Breaches
SecureWorld News
OCTOBER 8, 2023
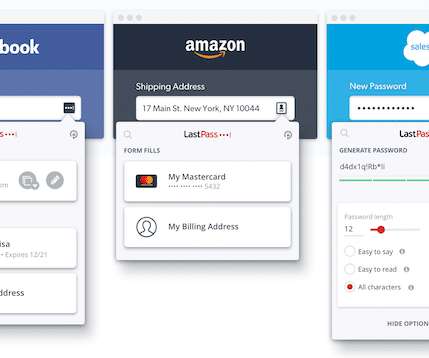
Use the administrator account only for maintenance, software installation, or firmware updates. Opt for strong, hard-to-crack passwords. Consider using dedicated password manager apps. Attention should be paid to protecting routers and updating their firmware. Fully utilize firewall capabilities.


















Let's personalize your content