The source code of the BlackLotus UEFI Bootkit was leaked on GitHub
Security Affairs
JULY 14, 2023
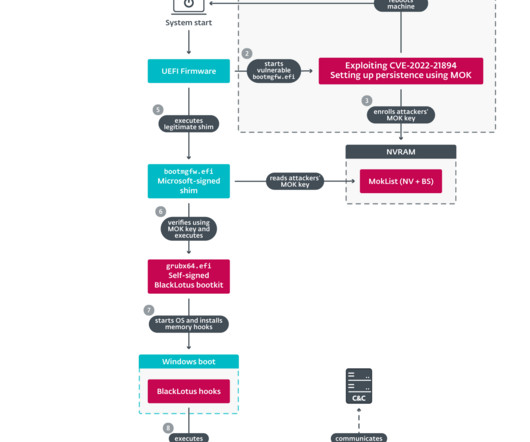
The source code for the BlackLotus UEFI bootkit has been published on GitHub and experts warn of the risks of proliferation of custom versions. Researchers from ESET discovered in March a new stealthy Unified Extensible Firmware Interface ( UEFI ) bootkit, named BlackLotus , that is able to bypass Secure Boot on Windows 11.




















Let's personalize your content