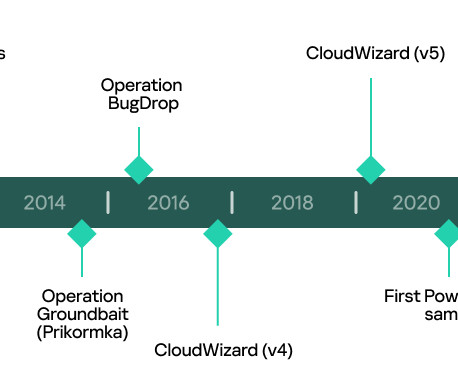
A deeper insight into the CloudWizard APT’s activity revealed a long-running activity
Security Affairs
MAY 23, 2023
In the latest campaign uncovered by Kaspersky, the APT group, used a modular framework dubbed CloudWizard that supports spyware capabilities, including taking screenshots, microphone recording, harvesting Gmail inboxes, and keylogging. Further analysis revealed that the actor behind the above operations has been active since at least 2008.












Let's personalize your content