WizCase Report: Vulnerabilities found in WD My Book, NetGear Stora, SeaGate Home, Medion LifeCloud NAS
Security Affairs
OCTOBER 20, 2018
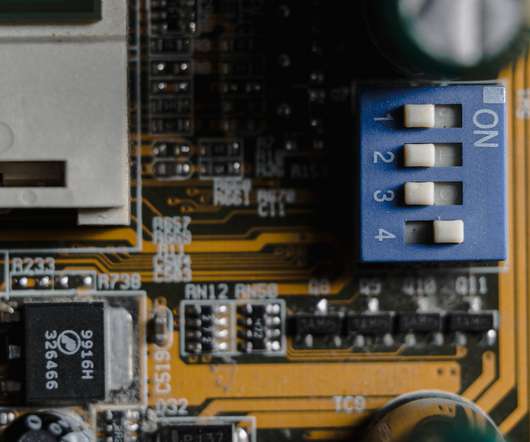
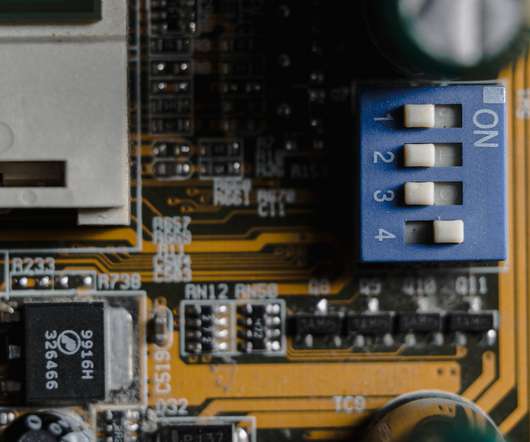
Meaning, authentication bypasses weren’t enough. All the php files were encrypted using IONCube which has a known public decoder and given the version used was an old one, decoding the files didn’t take long. After decoding the files , most of the API endpoints and the web interface were not accessible without authentication.














Let's personalize your content