Russia-linked InvisiMole APT targets state organizations of Ukraine
Security Affairs
MARCH 21, 2022
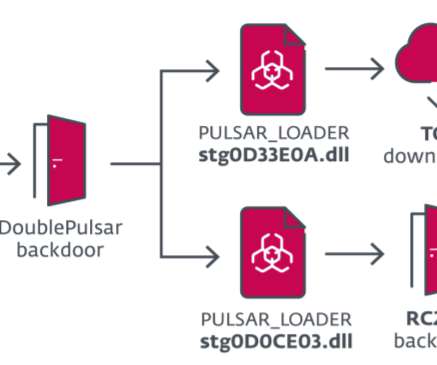
Then the backdoor contacts the command-and-control (C2) server to downloads and executes other malicious payloads, including the TunnelMole, malware that abuses the DNS protocol to establish a tunnel for malicious purposes, and RC2FM and RC2CL. The LoadEdge backdoor maintains persistence through the Windows registry.












Let's personalize your content