Enemybot, a new DDoS botnet appears in the threat landscape
Security Affairs
APRIL 17, 2022
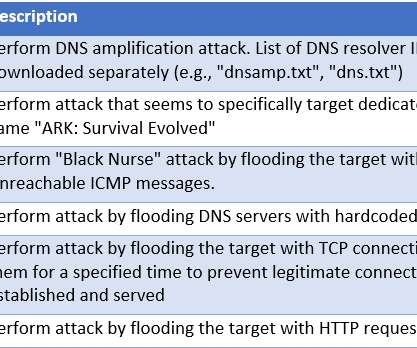
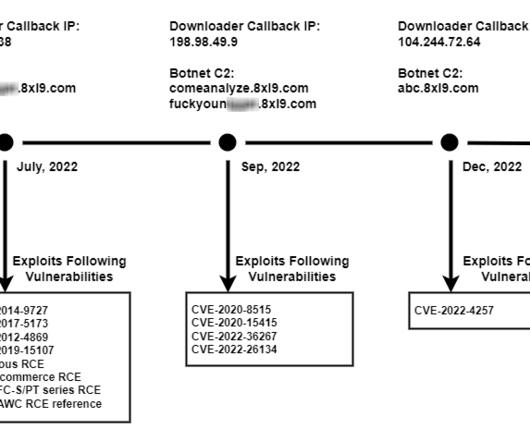
Enemybot is a DDoS botnet that targeted several routers and web servers by exploiting known vulnerabilities. Researchers from Fortinet discovered a new DDoS botnet, tracked as Enemybot, that has targeted several routers and web servers by exploiting known vulnerabilities. Upon installing the threat, the bot drops a file in /tmp/.pwned































Let's personalize your content