China-linked LightBasin group accessed calling records from telcos worldwide
Security Affairs
OCTOBER 20, 2021
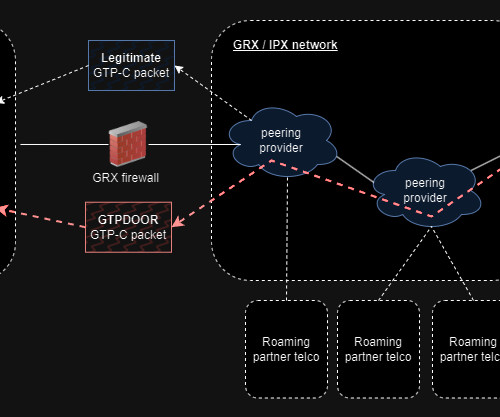
The cyberespionage group has been active since at least 2016, according to the CrowdStrike researchers it is using a very sophisticated toolset. CrowdStrike researchers reported that at least 13 telecommunication companies were compromised by since 2019. ” reads the report published by Crowdstrike.



























Let's personalize your content