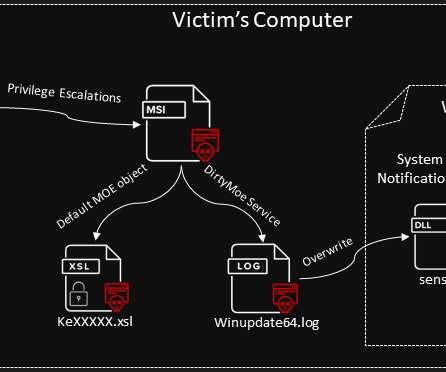
DirtyMoe botnet infected 100,000+ Windows systems in H1 2021
Security Affairs
JUNE 22, 2021
The Windows botnet has been active since late 2017, it was mainly used to mine cryptocurrency, but it was also involved in DDoS attacks in 2018. Experts pointed out that the number of infected systems could be far greater because data provided by AVAST are only related to systems running their antivirus solution.






















Let's personalize your content