Tricky Phish Angles for Persistence, Not Passwords
Krebs on Security
JANUARY 7, 2020
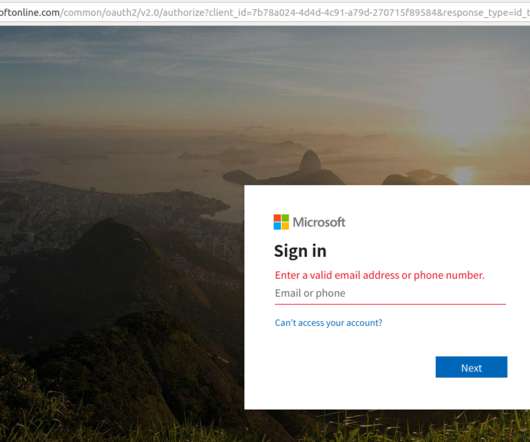
Late last year saw the re-emergence of a nasty phishing tactic that allows the attacker to gain full access to a user’s data stored in the cloud without actually stealing the account password. com — is different from the one I saw in late December, but it was hosted at the same Internet address as officesuited[.]com
















Let's personalize your content