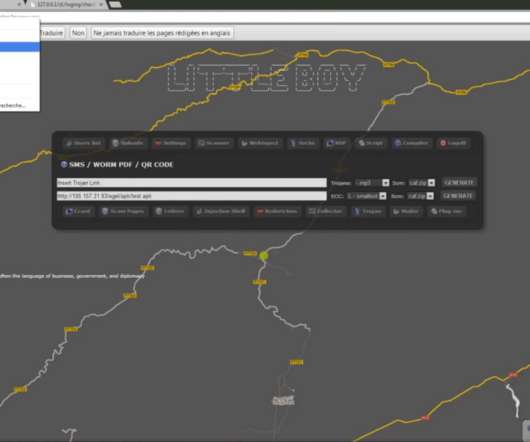
French Firms Rocked by Kasbah Hacker?
Krebs on Security
MARCH 2, 2020
In 2018, security intelligence firm HYAS discovered a malware network communicating with systems inside of a French national power company. When it didn’t hear from French authorities after almost a week, HYAS asked the dynamic DNS provider to “ sinkhole ” the malware network’s control servers. .























Let's personalize your content