Understanding Brute Force Attacks: The Persistent Threat in Cybersecurity
Webroot
APRIL 2, 2024
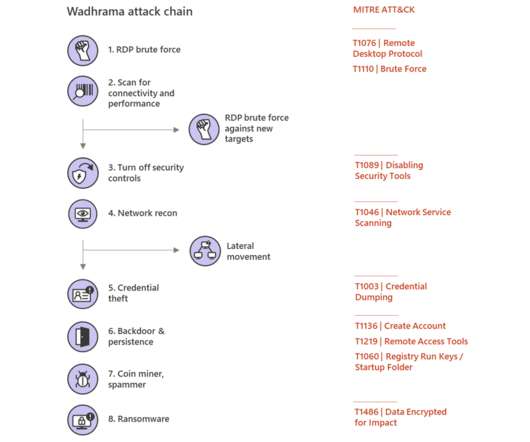
A brute force attack is a cyber attack where the attacker attempts to gain unauthorized access to a system or data by systematically trying every possible combination of passwords or keys. There are many already leaked password lists that are commonly used, and they grow after every breach. What is a Brute Force Attack?




























Let's personalize your content