Web Hacking Service ‘Araneida’ Tied to Turkish IT Firm
Krebs on Security
DECEMBER 19, 2024
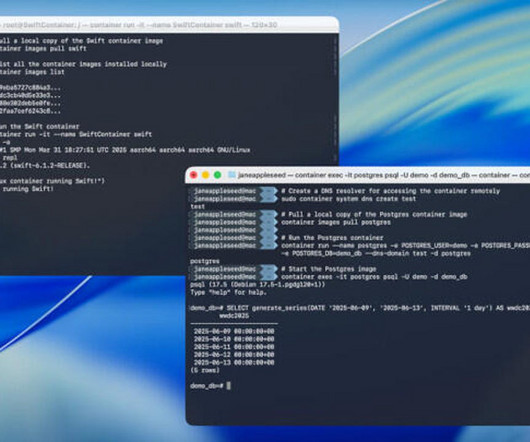
Cyber threat analysts at Silent Push said they recently received reports from a partner organization that identified an aggressive scanning effort against their website using an Internet address previously associated with a campaign by FIN7 , a notorious Russia-based hacking group. . ” Orn advertising Araneida Scanner in Feb.













































Let's personalize your content