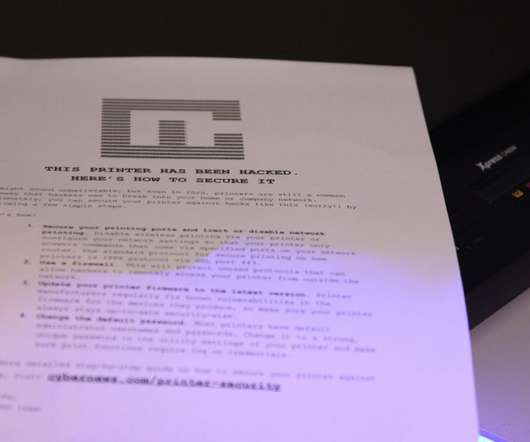
Experts hacked 28,000 unsecured printers to raise awareness of printer security issues
Security Affairs
AUGUST 27, 2020
Most of us already know the importance of using antivirus , anti-malware, and VPNs to secure our computers, phones, and other devices against potential attacks. Or they can simply use these printers to mine cryptocurrency, ramping up their victims’ electricity bills in the process. Update your printer firmware to the latest version.













Let's personalize your content