Detecting browser data theft using Windows Event Logs
Google Security
APRIL 30, 2024
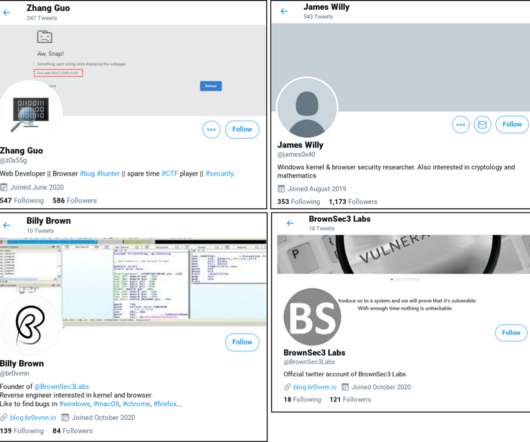
Where it is not possible to prevent the theft of credentials and cookies by malware, the next best thing is making the attack more observable by antivirus, endpoint detection agents, or enterprise administrators with basic log analysis tools. Export the event logs to your backend system. Create detection logic to detect theft.











































Let's personalize your content