Experts link the Black Basta ransomware operation to FIN7 cybercrime gang
Security Affairs
NOVEMBER 3, 2022
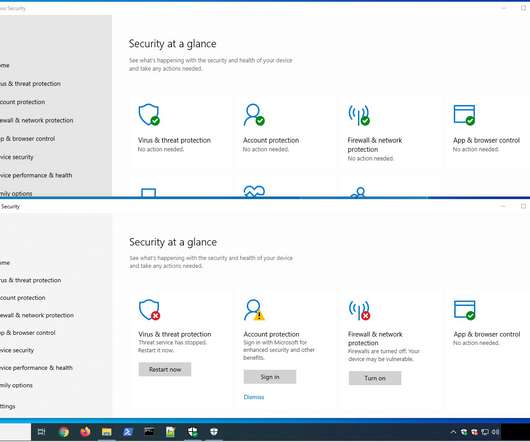
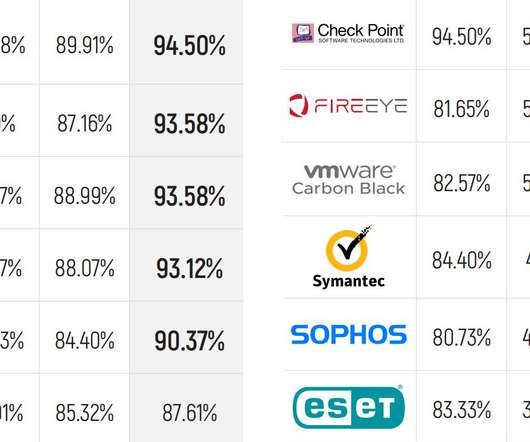
Sentinel Labs found evidence that links the Black Basta ransomware gang to the financially motivated hacking group FIN7. Security researchers at Sentinel Labs shared details about Black Basta ‘s TTPs and assess it is highly likely the ransomware operation has ties with FIN7. bat WindowsILUg69ql2.bat













Let's personalize your content