Calendar Meeting Links Used to Spread Mac Malware
Krebs on Security
FEBRUARY 28, 2024
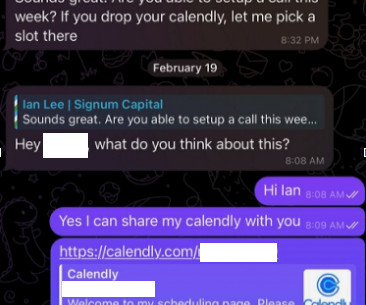
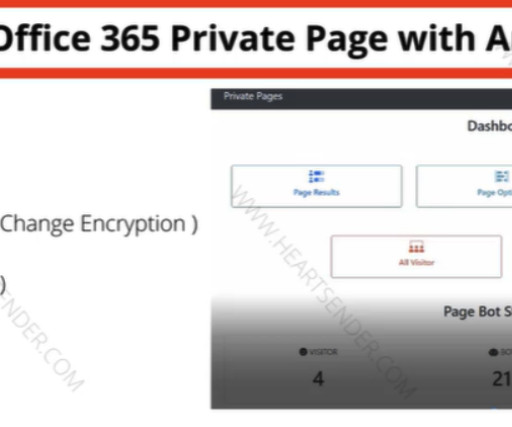
But clicking the meeting link provided by the scammers prompts the user to run a script that quietly installs malware on macOS systems. KrebsOnSecurity recently heard from a reader who works at a startup that is seeking investment for building a new blockchain platform for the Web.










Let's personalize your content