SHARING INTEL: Here’s why it has become so vital to prioritize the security-proofing of APIs
The Last Watchdog
NOVEMBER 30, 2021
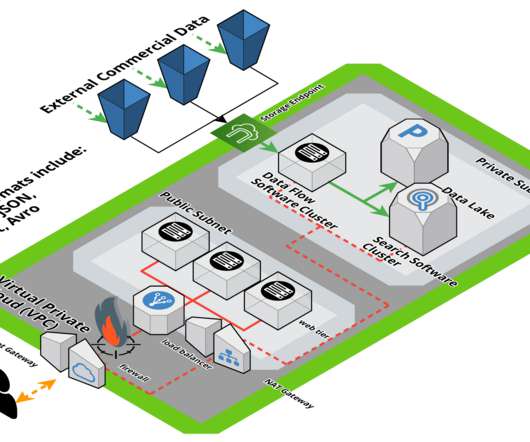
This summer Gartner designated API security as a stand-alone pillar in its security reference architecture, not just an add-on component to other systems. Many organizations, for instance, continue to rely heavily on legacy firewalls and WAFs, which, of course, is precisely where Capital One went wrong.














Let's personalize your content