DDoS Attacks Skyrocket, Kaspersky Researchers Say
eSecurity Planet
NOVEMBER 11, 2021
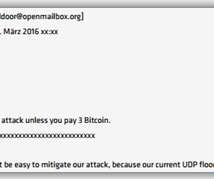
Distributed denial of service (DDoS) attacks soared in the third quarter, giving organizations yet another cyber threat to worry about. Even the slowest days saw 500 DDoS attacks; the busiest day, Aug. Also read: How to Stop DDoS Attacks: 6 Tips for Fighting DDoS Attacks. DDoS Attackers Target Middleboxes, UDP.













Let's personalize your content