Mirai-based DDoS botnet IZ1H9 added 13 payloads to target routers
Security Affairs
OCTOBER 11, 2023
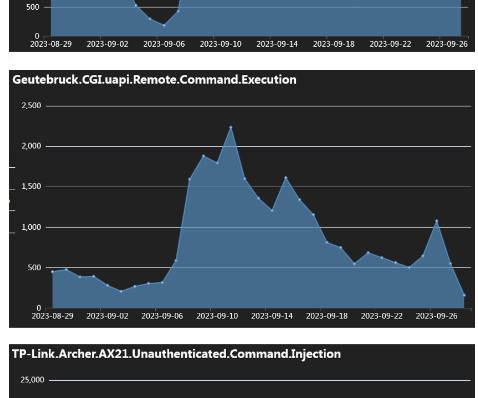
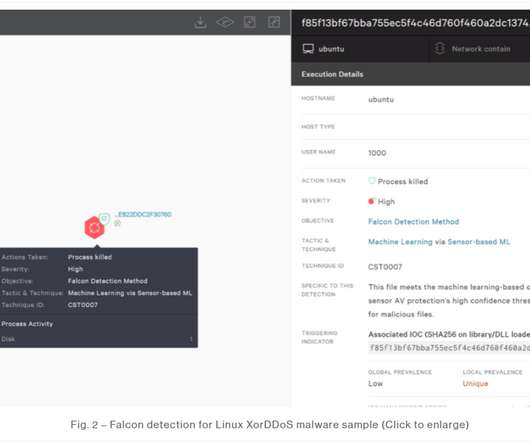
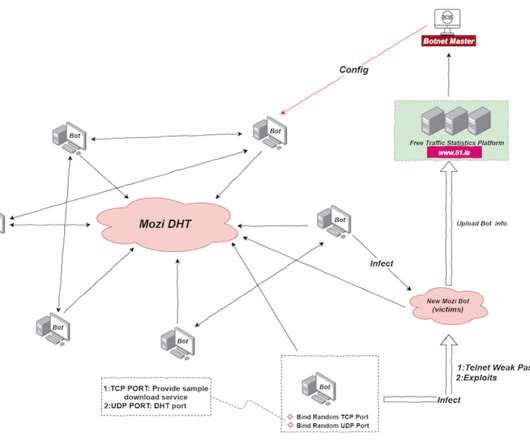
A Mirai-based DDoS botnet tracked as IZ1H9 has added thirteen new exploits to target routers from different vendors, including D-Link, Zyxel, and TP-Link. Upon executing the script, it deletes logs and downloads and executes various bot clients to target specific Linux architectures. ” reads the analysis published by Fortinet.
















Let's personalize your content