Giant Tiger breach sees 2.8 million records leaked
Malwarebytes
APRIL 16, 2024
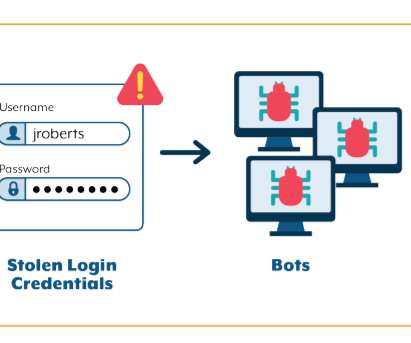
million records to a hacker forum, claiming they originated from a March 2024 hack at Canadian retail chain Giant Tiger. In March, one of Giant Tiger‘s vendors, a company used to manage customer communications and engagement, suffered a cyberattack, which impacted Giant Tiger, as reported by CBC. Watch out for fake vendors.



















Let's personalize your content