How to Write Spotless Job Description to Attract Cybersecurity Pros to Your Business
CyberSecurity Insiders
FEBRUARY 9, 2021
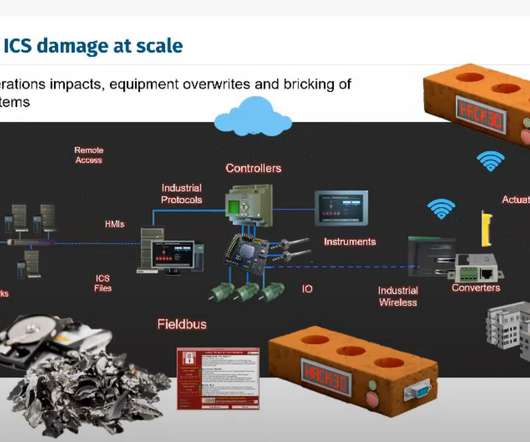
Whether you specialize in SaaS, outsource your services or operate as a physical goods trader in the B2B sector, the risk of cybersecurity intrusions prevails. Improved brand reputation and trust of your B2B network associates with their data. Firewall administration and maintenance. System administration and maintenance.



















Let's personalize your content