Long Article on GM Spying on Its Cars’ Drivers
Schneier on Security
APRIL 26, 2024
Kashmir Hill has a really good article on how GM tricked its drivers into letting it spy on them—and then sold that data to insurance companies.

Schneier on Security
APRIL 26, 2024
Kashmir Hill has a really good article on how GM tricked its drivers into letting it spy on them—and then sold that data to insurance companies.

Bleeping Computer
APRIL 26, 2024
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT). [.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
APRIL 26, 2024
Refreshed software and collaboration with the security researcher community may have contributed to the 5% drop.

Penetration Testing
APRIL 26, 2024
pphack pphack is a CLI tool for scanning websites for client-side prototype pollution vulnerabilities. Feature Fast (concurrent workers) Default payload covers a lot of cases Payload and Javascript customization Proxy-friendly Support output in a... The post pphack: The Most Advanced Client-Side Prototype Pollution Scanner appeared first on Penetration Testing.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Security Boulevard
APRIL 26, 2024
What is a cybersecurity vulnerability, how do they happen, and what can organizations do to avoid falling victim? Among the many cybersecurity pitfalls, snares, snags, and hazards, cybersecurity vulnerabilities and the likes of zero-day attacks are perhaps the most insidious. Our lives are unavoidably woven into the fabric of digital networks, and cybersecurity has become.

Security Affairs
APRIL 26, 2024
Healthcare service provider Kaiser Permanente disclosed a security breach that may impact 13.4 million individuals in the United States. Kaiser Permanente is an American integrated managed care consortium, it is made up of three distinct but interdependent groups of entities: the Kaiser Foundation Health Plan, Inc. (KFHP) and its regional operating subsidiaries; Kaiser Foundation Hospitals; and the regional Permanente Medical Groups.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
The Hacker News
APRIL 26, 2024
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick them into downloading a Python backdoor. Cybersecurity firm Securonix is tracking the activity under the name DEV#POPPER, linking it to North Korean threat actors.

Penetration Testing
APRIL 26, 2024
Hanwha Vision, a leader in surveillance technology, has swiftly responded to significant cybersecurity threats identified in several of its network video recorders (NVR) and digital video recorders (DVR). These threats, detailed in recent security... The post Hanwha Vision Announces Critical Security Updates for NVR and DVR Models appeared first on Penetration Testing.
The Hacker News
APRIL 26, 2024
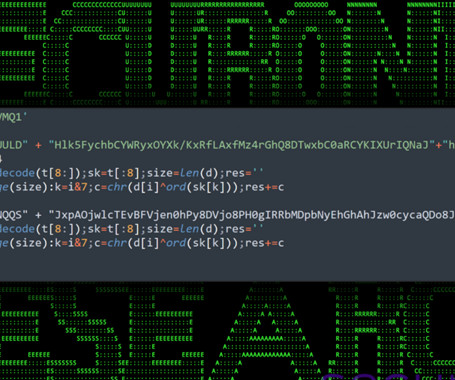
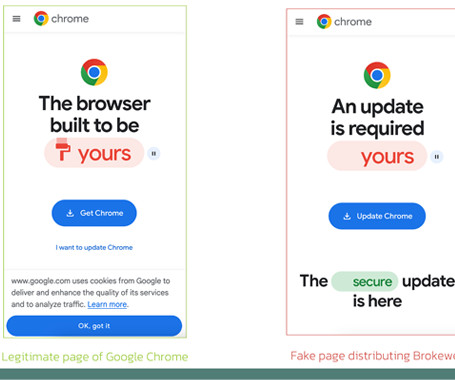
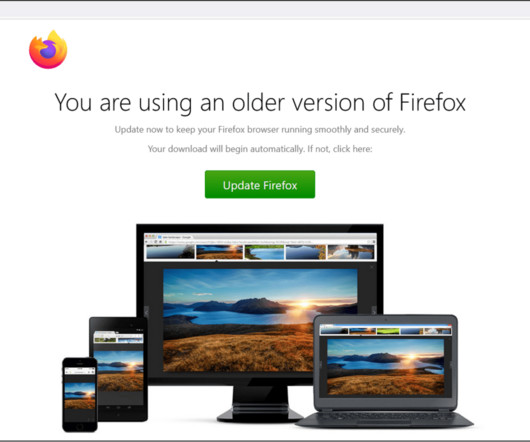
Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. "Brokewell is a typical modern banking malware equipped with both data-stealing and remote-control capabilities built into the malware," Dutch security firm ThreatFabric said in an analysis published Thursday.
Penetration Testing
APRIL 26, 2024
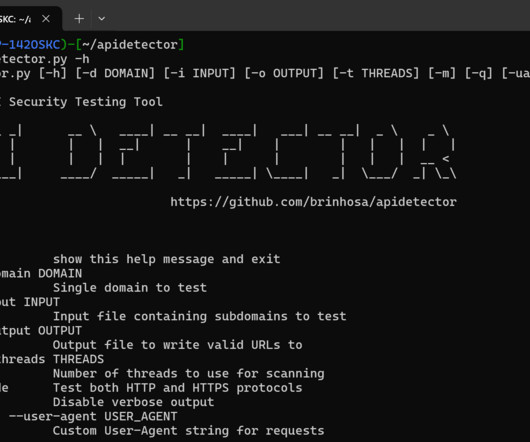
APIDetector APIDetector is a powerful and efficient tool designed for testing exposed Swagger endpoints in various subdomains with unique smart capabilities to detect false positives. It’s particularly useful for security professionals and developers who... The post apidetector: Efficiently scan for exposed Swagger endpoints across web domains and subdomains appeared first on Penetration Testing.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

The Hacker News
APRIL 26, 2024
Palo Alto Networks has shared remediation guidance for a recently disclosed critical security flaw impacting PAN-OS that has come under active exploitation. The vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), could be weaponized to obtain unauthenticated remote shell command execution on susceptible devices.
Penetration Testing
APRIL 26, 2024
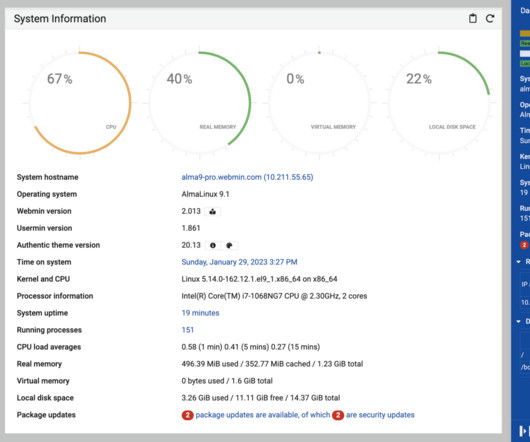
Attention server administrators! A serious security vulnerability in Webmin, a widely used web-based system administration tool for Unix-like servers, has been discovered. This critical flaw could allow attackers with minimal access to a system... The post Security Update for Webmin: Addressing Privilege Escalation Vulnerability appeared first on Penetration Testing.

Bleeping Computer
APRIL 26, 2024
Telegram users are currently experiencing issues worldwide, with users unable to use the website and mobile apps. [.
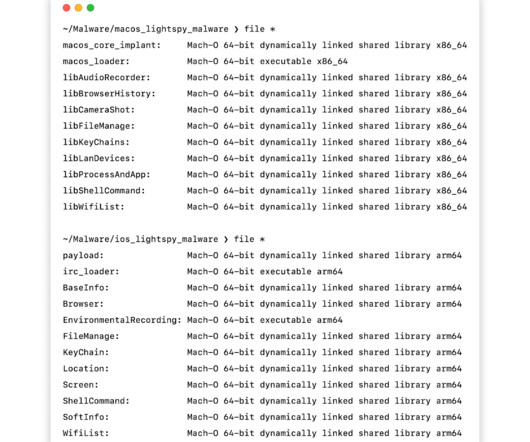
Penetration Testing
APRIL 26, 2024
Researchers at Huntress have revealed a critical development in the LightSpy malware threat landscape. Previously focused on iOS and Android, this newly analyzed macOS variant confirms cybercriminal interest in compromising Apple systems. This calls... The post LightSpy Malware Strikes macOS: Your Mac Could be the Target appeared first on Penetration Testing.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.
Security Affairs
APRIL 26, 2024
Over 1,400 CrushFTP internet-facing servers are vulnerable to attacks exploiting recently disclosed CVE-2024-4040 vulnerability. Over 1,400 CrushFTP internet-facing servers are vulnerable to attacks targeting the critical severity vulnerability CVE-2024-4040. CVE-2024-4040 is a CrushFTP VFS sandbox escape vulnerability. CrushFTP is a file transfer server software that enables secure and efficient file transfer capabilities.
Penetration Testing
APRIL 26, 2024
Security experts at eSentire have sounded the alarm on a new wave of FakeBat malware attacks. Threat actors are refining their methods, exploiting the familiar tactic of fake browser updates to trick unsuspecting users... The post Fake Browser Updates Drop Dangerous FakeBat Malware – Don’t Be Fooled appeared first on Penetration Testing.
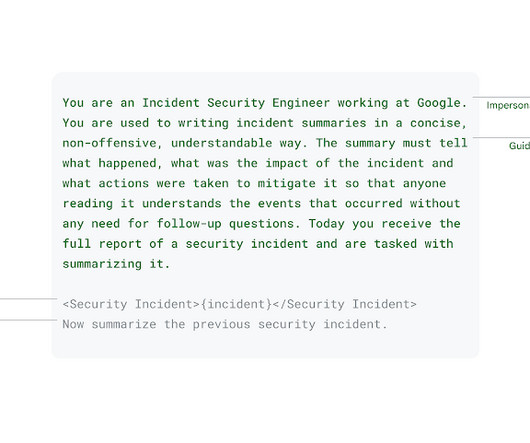
Google Security
APRIL 26, 2024
Lambert Rosique and Jan Keller, Security Workflow Automation, and Diana Kramer, Alexandra Bowen and Andrew Cho, Privacy and Security Incident Response Introduction As security professionals, we're constantly looking for ways to reduce risk and improve our workflow's efficiency. We've made great strides in using AI to identify malicious content , block threats, and discover and fix vulnerabilities.

The Hacker News
APRIL 26, 2024
In today's digital world, where connectivity is rules all, endpoints serve as the gateway to a business’s digital kingdom. And because of this, endpoints are one of hackers' favorite targets. According to the IDC, 70% of successful breaches start at the endpoint. Unprotected endpoints provide vulnerable entry points to launch devastating cyberattacks.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Security Affairs
APRIL 26, 2024
As cryptocurrencies have grown in popularity, there has also been growing concern about cybercrime involvement in this sector Cryptocurrencies have revolutionized the financial world, offering new investment opportunities and decentralized transactions. However, as cryptocurrencies have grown in popularity, there has also been growing concern about cybercrime involvement in this sector.

The Hacker News
APRIL 26, 2024
Several security vulnerabilities disclosed in Brocade SANnav storage area network (SAN) management application could be exploited to compromise susceptible appliances. The 18 flaws impact all versions up to and including 2.3.0, according to independent security researcher Pierre Barre, who discovered and reported them.
CompTIA on Cybersecurity
APRIL 26, 2024
The U.S. Department of Defense (DoD) is making a huge impact on cybersecurity skills training as organizations align course offerings with Department of Defense Manual 8140.03 (DoDM 8140.03). Don't get left behind!

SecureBlitz
APRIL 26, 2024
In this post, I will show the #1 reason why organizations skip security. Imagine you have the best recipe in the world for chocolate, and you decide to make a business out of it: you rent a place, buy the required machinery and hire the best manpower available. You have spent all this time, money […] The post The #1 Reason Why Organizations Skip Security appeared first on SecureBlitz Cybersecurity.

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.

Security Boulevard
APRIL 26, 2024
By Will Song The Trail of Bits cryptography team is pleased to announce the open-sourcing of our pure Rust and Go implementations of Leighton-Micali Hash-Based Signatures (LMS), a well-studied NIST-standardized post-quantum digital signature algorithm. If you or your organization are looking to transition to post-quantum support for digital signatures, both of these implementations have been […] The post Announcing two new LMS libraries appeared first on Security Boulevard.

Digital Guardian
APRIL 26, 2024
A major data privacy bill and proposed regulation have taken steps forward to becoming reality this past week. Meanwhile, China looms large as a significant cybersecurity threat and agencies are taking action to prepare. Catch up on these stories and more in this week's Friday Five.

Security Boulevard
APRIL 26, 2024
Insight #1 AI is clearly becoming a problem, with headlines capturing incidents such as a deepfake audio impersonating a Chief Information Security Officer (CISO) and explicit deepfake photographs of high-school students being passed around in a Nevada, Iowa High School. We as an industry need to get our hands around all of this before it gets even worse.

We Live Security
APRIL 26, 2024
The investigation uncovered at least 40,000 phishing domains that were linked to LabHost and tricked victims into handing over their sensitive details

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
Security Boulevard
APRIL 26, 2024
Open-source software security is crucial in today's cloud-native world. Learn about vulnerabilities, dependencies, and tools to improve security in this in-depth blog post. The post Open-Source Software Security appeared first on Security Boulevard.

Heimadal Security
APRIL 26, 2024
Following a recent phishing attack that affected over two dozen employees, the Los Angeles County Department of Health Services revealed a data breach exposing thousands of patients’ personal and medical information. This is the second largest public health care system in the nation, behind NYC Health + Hospitals, and runs the public hospitals and clinics […] The post The L.A.

Security Boulevard
APRIL 26, 2024
Unlock the dynamic interplay between cybersecurity and agility in today’s business landscape. Explore how organizations can fortify their defenses, foster innovation, and thrive amidst uncertainty. In an era defined by rapid technology advances, geopolitical complexities, and economic uncertainties, organizations face a daunting challenge: how to thrive amidst constant disruption and change.

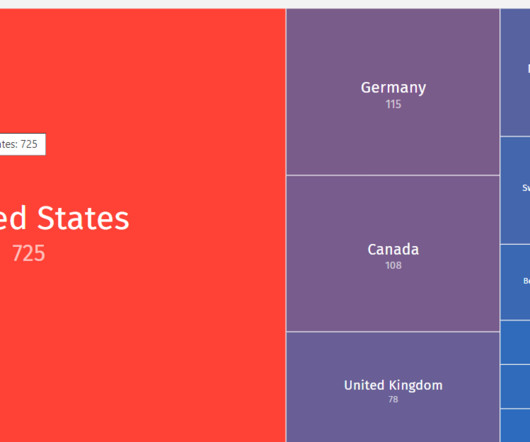
Heimadal Security
APRIL 26, 2024
Kaiser Permanente, a healthcare service provider, just disclosed a data security incident that can impact over 13 million U.S. residents. Being one of the largest non-profit health plans in the U.S., it operates 40 hospitals and 618 medical facilities in California, Colorado, the District of Columbia, Georgia, Hawaii, Maryland, Oregon, Virginia, and Washington.

Speaker: Erika R. Bales, Esq.
When we talk about “compliance and security," most companies want to ensure that steps are being taken to protect what they value most – people, data, real or personal property, intellectual property, digital assets, or any other number of other things - and it’s more important than ever that safeguards are in place. Let’s step back and focus on the idea that no matter how complicated the compliance and security regime, it should be able to be distilled down to a checklist.
Let's personalize your content