GUEST ESSAY: Here’s how Secure Access Service Edge — ‘SASE’ — can help, post Covid-19
The Last Watchdog
DECEMBER 13, 2020
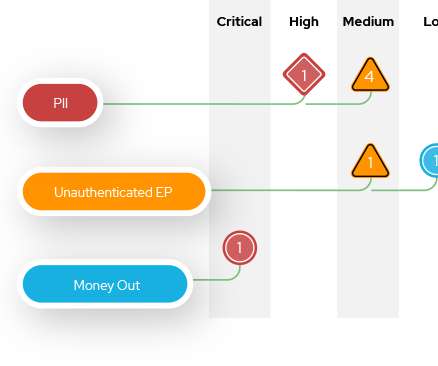
It incorporates zero-trust technologies and software-defined wide area networking (SD-WAN). It can also deploy web filtering, threat prevention, DNS security, sandboxing, data loss prevention, next-generation firewall policies, information security and credential theft prevention. . But it much further. The cyber threats landscape.



















Let's personalize your content