5 Ways to Strengthen the Weak Link in Cybersecurity
IT Security Guru
JUNE 7, 2024
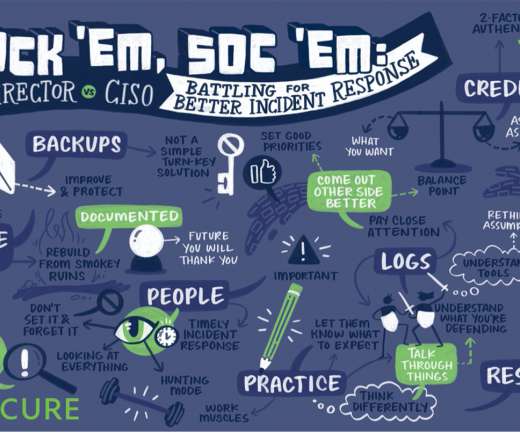
Backup Your Data Experiencing data loss, particularly as a consequence of a cyberattack , can spell disaster for your business. Engaging in data backup practices guarantees the preservation of your crucial information and assets even amidst unfavorable circumstances, be it cyber threats or unexpected calamities.




























Let's personalize your content