Unanswered Questions Loom Over Cyber Attacks on M&S, Co-op & Harrods
Jane Frankland
MAY 3, 2025
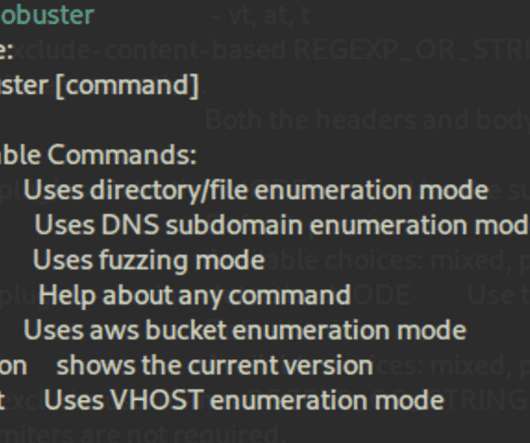
Allegedly orchestrated by the same group known as Scattered Spider, these attacks highlight the significant challenges even the most respected and established brands face in defending against modern cyber threats. Then, the focus of cyber attacks on retailers, and what lessons must be learned by business leaders and customers.













































Let's personalize your content