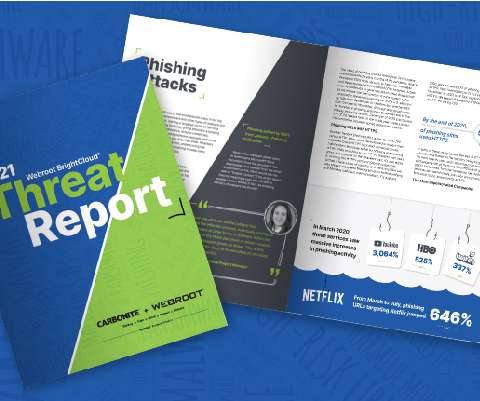
Ransomware, BEC and Phishing Still Top Concerns, per 2021 Threat Report
Webroot
APRIL 21, 2021
Although cybercriminal activity throughout 2020 was as innovative as ever, some of the most noteworthy threat activity we saw came from the old familiar players, namely ransomware, business email compromise (BEC) and phishing. COVID-19 definitely affected phishing in very visible ways.















Let's personalize your content