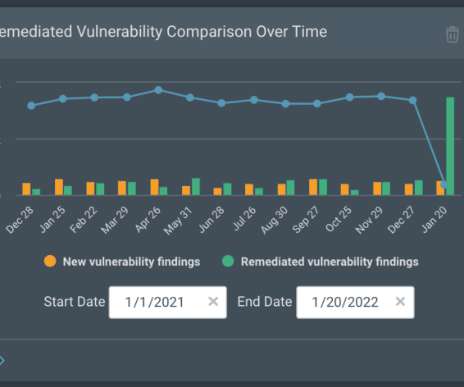
Average enterprise storage/backup device has 14 vulnerabilities, three high or critical risks
CSO Magazine
MARCH 22, 2023
The average enterprise storage and backup device has 14 vulnerabilities, three of which are high or critical risk that could present a significant compromise if exploited. To read this article in full, please click here















































Let's personalize your content