Operation Phobos Aetor: Police dismantled 8Base ransomware gang
Security Affairs
FEBRUARY 11, 2025
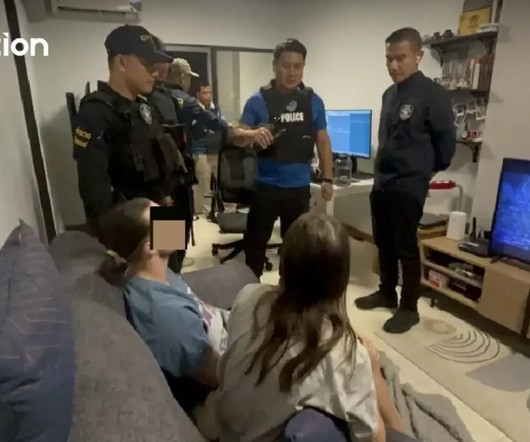
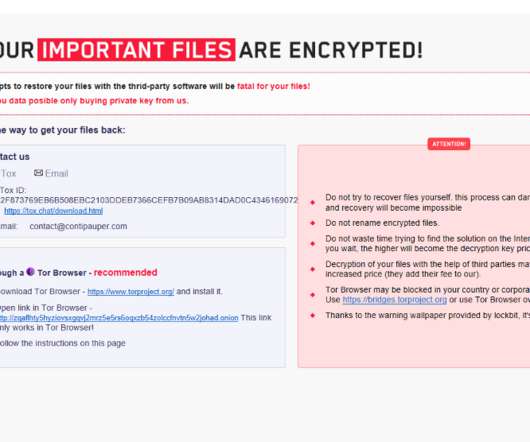
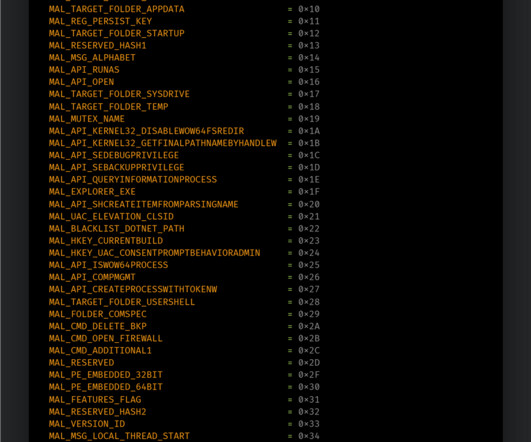
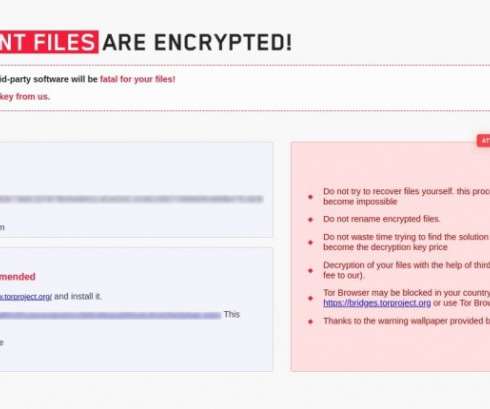
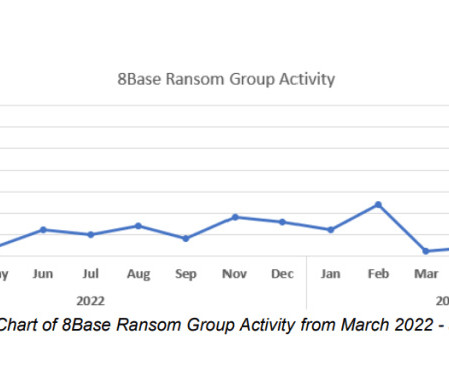
Authorities dismantled the 8Base ransomware gang, shutting down its dark web data leak and negotiation sites. An international law enforcement operation, codenamed Operation Phobos Aetor, dismantled the 8Base ransomware gang. The ransomware component is then decrypted and loaded into the SmokeLoader process memory.
















Let's personalize your content