Weakness at the Network Edge: Mandiant Examines 2022’s Zero-Day Exploits
eSecurity Planet
MARCH 27, 2023
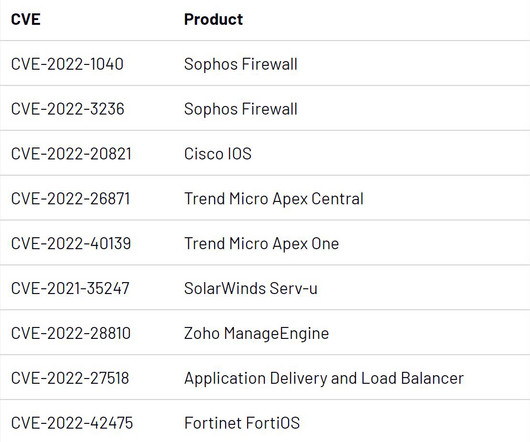
A quarter were financially motivated, and three of those were linked to ransomware operations. Targeting Firewalls and IPS/IDS Appliances In the case of CVE-2022-42475, a flaw in Fortinet’s FortiOS SSL-VPN, Mandiant observed a Chinese state-sponsored group exploiting the vulnerability in late 2022.









Let's personalize your content