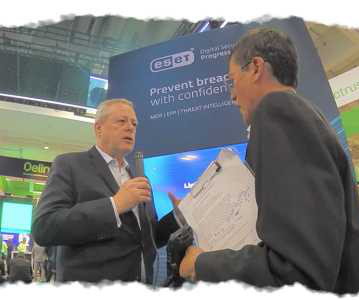
RSAC Fireside Chat: Operationalizing diverse security to assure customers, partners–and insurers
The Last Watchdog
JUNE 11, 2025
Related: Getting the most from cyber insurance At RSAC 2025, I met with ESET Chief Security Evangelist Tony Anscombe to trace a quiet but growing convergence: endpoint defense, cyber insurance, and monoculture risk are no longer separate concerns. Cyber insurers want it. MSSPs need it.





























Let's personalize your content