Tackling Cyber Threats: Is AI Cybersecurity Our Only Hope?
Jane Frankland
MAY 8, 2024
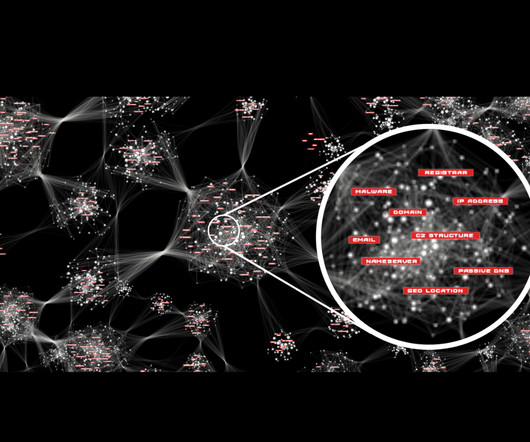
Could artificial intelligence (AI) be the key to outsmarting cyber threats in an increasingly connected world? Constantly Evolving Threats Just as the night follows the day, the world of cybersecurity is no stranger to constant change and adaptation. Is it our only hope for survival?These















































Let's personalize your content