6 Business functions that will benefit from cybersecurity automation
CyberSecurity Insiders
OCTOBER 28, 2021
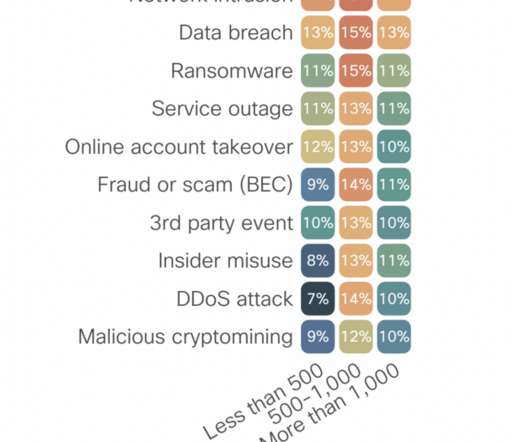
Enterprises and small businesses alike are facing challenges that impact their ability to maintain adequate cybersecurity. Budget constraints and limited staff are just a couple of reasons why businesses have become more susceptible to cyberattacks. The business case for automation.

























Let's personalize your content