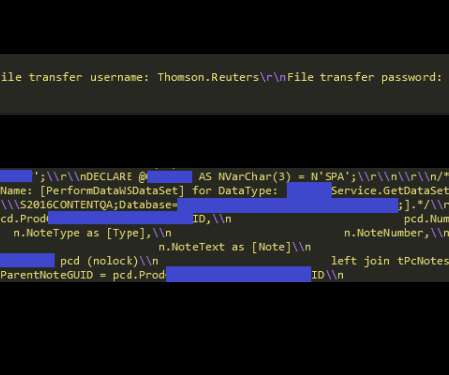
Thomson Reuters collected and leaked at least 3TB of sensitive data
Security Affairs
OCTOBER 27, 2022
“ElasticSearch is a very common and widely used data storage and is prone to misconfigurations, which makes it accessible to anyone. This instance left sensitive data open and was already indexed via popular IoT [internet of things] search engines. Cases like these raise questions about corporate data collection practices.









Let's personalize your content