Education in Secure Software Development
Schneier on Security
AUGUST 1, 2024
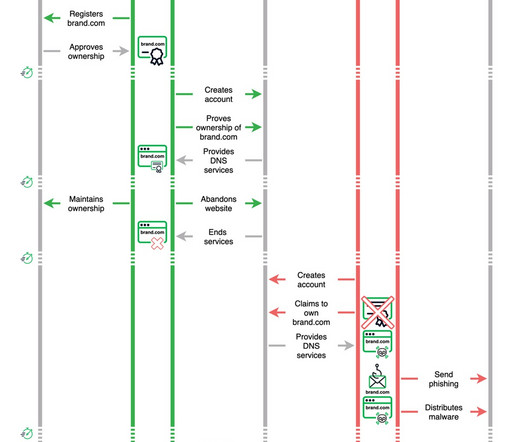
The Linux Foundation and OpenSSF released a report on the state of education in secure software development. …many developers lack the essential knowledge and skills to effectively implement secure software development. Survey findings outlined in the report show nearly one-third of all professionals directly involved in development and deployment system operations, software developers, committers, and maintainers self-report feeling unfamiliar with secure software development practice








































Let's personalize your content