RSAC Fireside Chat: Counteracting Putin’s weaponizing of ransomware — with containment
The Last Watchdog
MAY 20, 2023
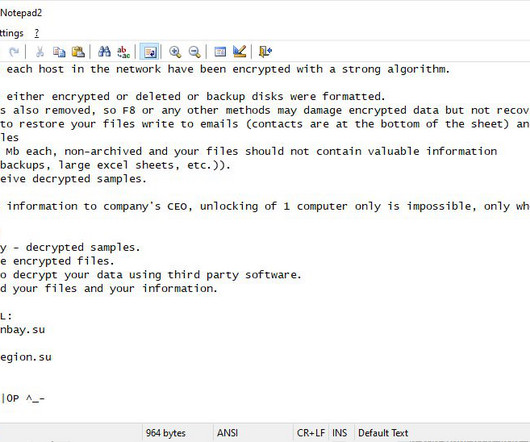
The ransomware plague endures — and has arisen as a potent weapon in geopolitical conflicts. Related: The Golden Age of cyber espionage Cyber extortion remains a material threat to organizations of all sizes across all industries. Ransomware purveyors have demonstrated their capability to endlessly take advantage of a vastly expanded network attack surface – one that will only continue to expand as the shift to massively interconnected digital services accelerates.









Let's personalize your content