How to Identify and Avoid Holiday Phishing Scams
Identity IQ
AUGUST 31, 2023
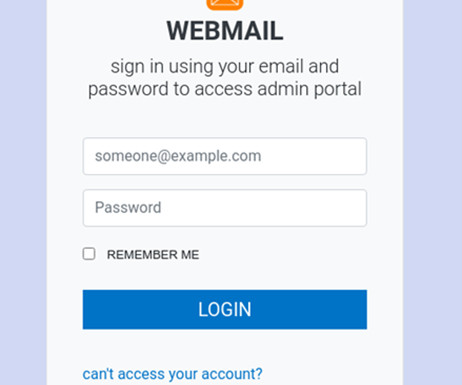
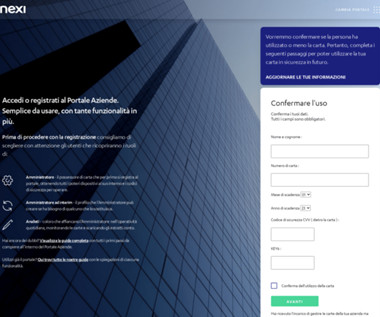
How to Identify and Avoid Holiday Phishing Scams IdentityIQ The holiday season brings joy, celebrations, and… a surge in online scams. Holiday phishing scams are an ongoing issue that ramps up when folks are feeling the most festive. What Is a Phishing Scam? How Does Phishing Work? Their goal?










































Let's personalize your content