Is Your Small Business Safe Against Cyber Attacks?
CyberSecurity Insiders
MARCH 21, 2021
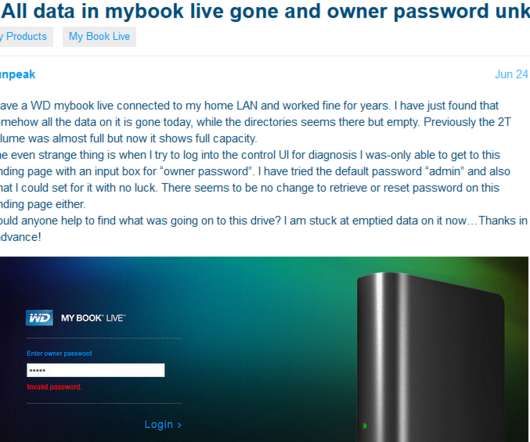
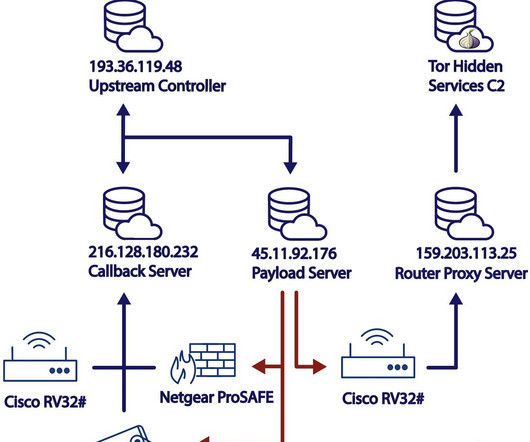
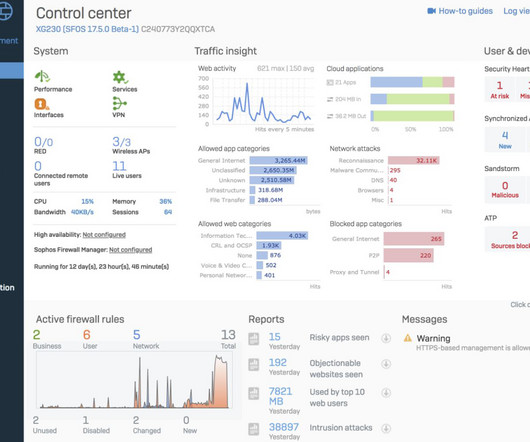
Just because you are running a small business doesn’t mean you are out of the reach of cybercriminals and hackers. In fact, small businesses are more susceptible to security breaches and cyberattacks because most often they dont expect the attack, thus are unprepared to handle the situation. Upgrade your IT set up.
























Let's personalize your content