Penetration Testing: What is it?
NetSpi Executives
APRIL 27, 2024
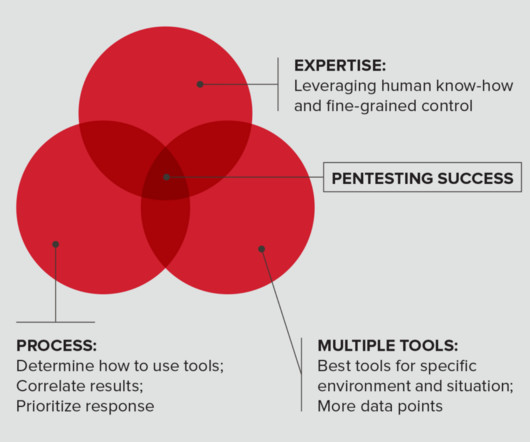
Table of Contents What is penetration testing? How penetration testing is done How to choose a penetration testing company How NetSPI can help Penetration testing enables IT security teams to demonstrate and improve security in networks, applications, the cloud, hosts, and physical locations.











Let's personalize your content