CrowdStrike 2024 Global Threat Report: 6 Key Takeaways
Tech Republic Security
FEBRUARY 26, 2024
Identity-based and social engineering attacks still take center stage, according to the CrowdStrike 2024 Global Threat Report.

Tech Republic Security
FEBRUARY 26, 2024
Identity-based and social engineering attacks still take center stage, according to the CrowdStrike 2024 Global Threat Report.
eSecurity Planet
SEPTEMBER 15, 2022
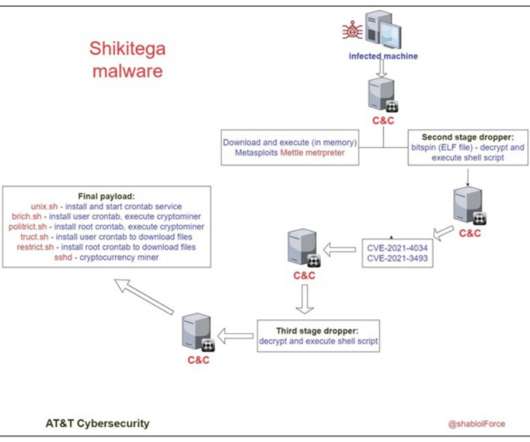
This strategy seems to be a trade-off, as such services are way easier to take down by authorities, but it allows bypassing network security products that don’t block legitimate providers. AT&T labs provided a list of IoCs (indicators of compromise) that system administrators can use to add specific rules to security solutions.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
AUGUST 8, 2022
The Verizon report includes a startling statistic that appeared in the 2022 Thales Data Threat Report that “two-fifths of organizations are not confident that their current security systems could effectively secure the remote work environment.”. Security is a shared responsibility. Data Security.

Webroot
DECEMBER 14, 2020
Home networks and their configurations are diverse. Personal devices are often used for work and, as we saw in our 2020 Threat Report, are twice as likely as business devices to encounter infections. Hal Lonas, CTO and SVP of SMB engineering, Carbonite + Webroot. security analyst, Carbonite + Webroot.

eSecurity Planet
JANUARY 9, 2023
Discover security issues as part of the software development lifecycle (SDLC) as soon as possible. With over 450 pre-configured templates, speedily understand where you have threats. Reporting and troubleshooting capabilities can be customized to meet particular needs and are exportable in multiple formats.
Let's personalize your content