Russia-linked APT28 has been scanning vulnerable email servers in the last year
Security Affairs
MARCH 20, 2020
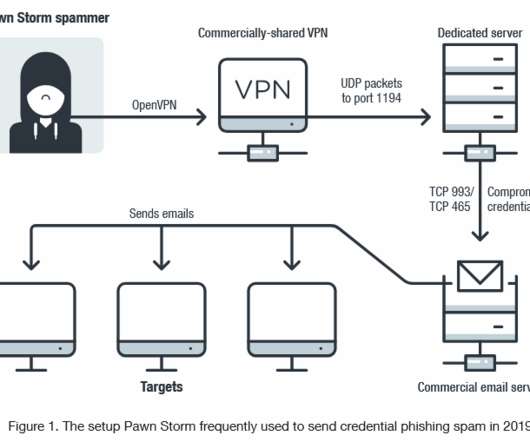
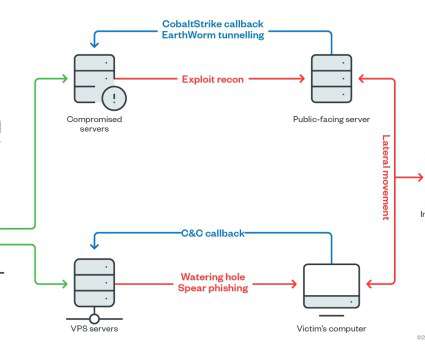
The APT28 group (aka Fancy Bear , Pawn Storm , Sofacy Group , Sednit , and STRONTIUM ) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. “This report aims to shed light on some of Pawn Storm’s attacks that did not use malware in the initial stages.










Let's personalize your content