Fake Lawsuit Threat Exposes Privnote Phishing Sites
Krebs on Security
APRIL 4, 2024
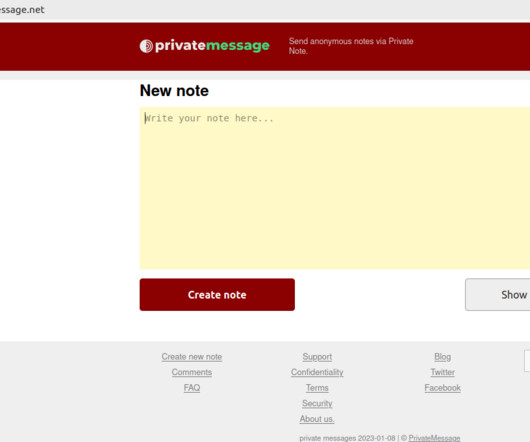
Launched in 2008, privnote.com employs technology that encrypts each message so that even Privnote itself cannot read its contents. For example, this account at Medium has authored more than a dozen blog posts in the past year singing the praises of Tornote as a secure, self-destructing messaging service. Among those is rustraitor[.]info















Let's personalize your content