Ask Fitis, the Bear: Real Crooks Sign Their Malware
Krebs on Security
JUNE 1, 2023
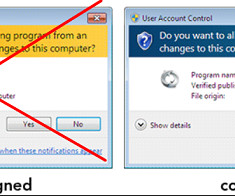
Code-signing certificates are supposed to help authenticate the identity of software publishers, and provide cryptographic assurance that a signed piece of software has not been altered or tampered with. “Antivirus software trusts signed programs more. ru in 2008. su from 2008. “Why do I need a certificate?”














Let's personalize your content