When Your Smart ID Card Reader Comes With Malware
Krebs on Security
MAY 17, 2022
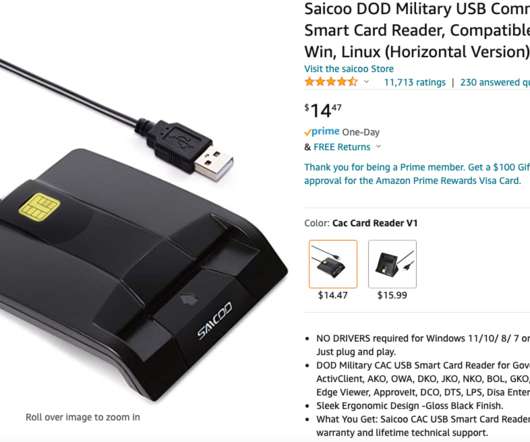
Out of an abundance of caution, Mark submitted Saicoo’s drivers file to Virustotal.com , which simultaneously scans any shared files with more than five dozen antivirus and security products. Virustotal reported that some 43 different security tools detected the Saicoo drivers as malicious. Don’t worry.”















Let's personalize your content