Fake Lawsuit Threat Exposes Privnote Phishing Sites
Krebs on Security
APRIL 4, 2024
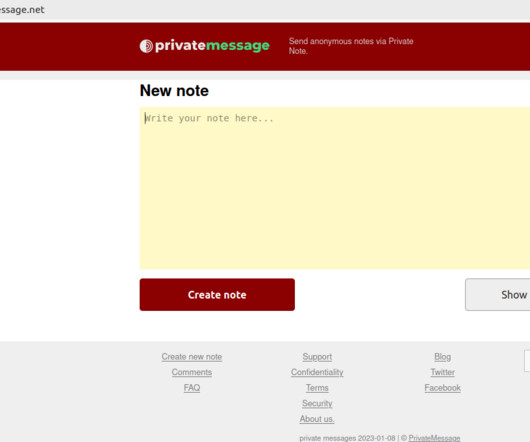
Launched in 2008, privnote.com employs technology that encrypts each message so that even Privnote itself cannot read its contents. Throughout 2023, Tornote was hosted with the Russian provider DDoS-Guard , at the Internet address 186.2.163[.]216. The real Privnote, at privnote.com. com , meternask[.]com

















Let's personalize your content