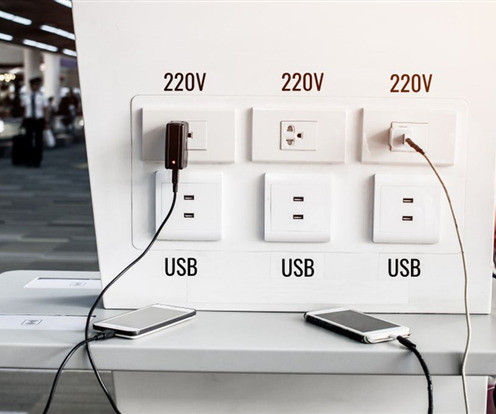
Don't plug your phone into a free charging station, warns FBI
Malwarebytes
APRIL 11, 2023
The term was first used by Brian Krebs in 2011 after a proof of concept was conducted at DEF CON by Wall of Sheep. There are crawlers that can search your phone for personally identifiable information (PII), account credentials, banking-related or credit card data in seconds. However, the chances of that happening are rather slim.










Let's personalize your content