Chinese Antivirus Firm Was Part of APT41 ‘Supply Chain’ Attack
Krebs on Security
SEPTEMBER 17, 2020
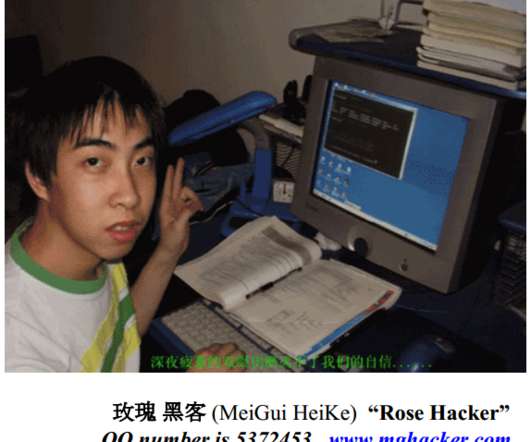
Justice Department this week indicted seven Chinese nationals for a decade-long hacking spree that targeted more than 100 high-tech and online gaming companies. One of the alleged hackers was first profiled here in 2012 as the owner of a Chinese antivirus firm. Image: FBI. Image: FBI.

















Let's personalize your content