Why We Still Haven’t Learned From the Target Data Breach a Decade Later
Security Boulevard
MAY 17, 2023
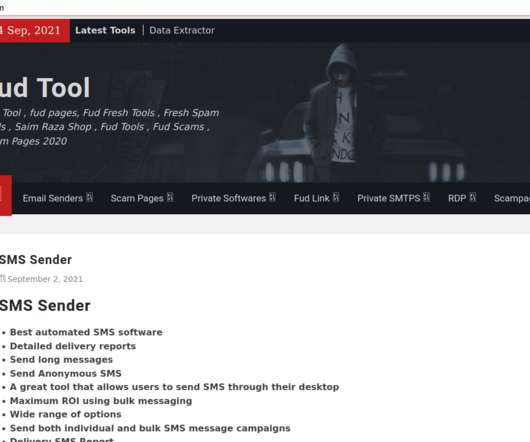
Most of these steps could’ve been blocked with the aid of DNS protection. It would be easy to chalk up this increase to the development and introduction of new advanced types of malware, but the surprising fact is that many of the same threats and exploits used in data breaches in 2013 are still being successfully employed 10 years later.












Let's personalize your content