5 pro-freedom technologies that could change the Internet
Malwarebytes
JULY 4, 2022
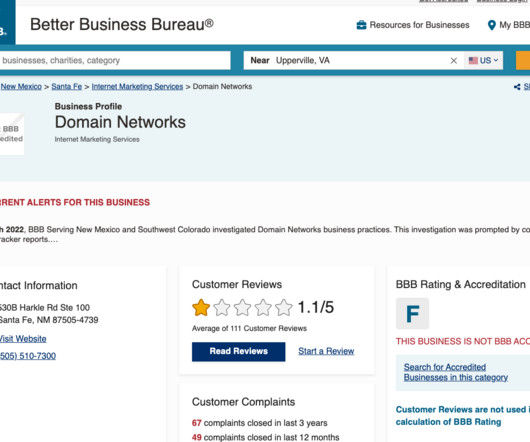
DNS encryption. DNS encryption plugs a gap that makes it easy to track the websites you visit. The domain name system (DNS) is a distributed address book that lists domain names and their corresponding IP addresses. Passwords are a great idea in theory that fail horribly in practice.
















Let's personalize your content